Hey Guys!
Spending the majority of my time online, I often encounter all kinds of “Top N-list of Something-Something” so I decided it was about time to dip my own toes in such type of article. Let’s see how this one takes off 🙂
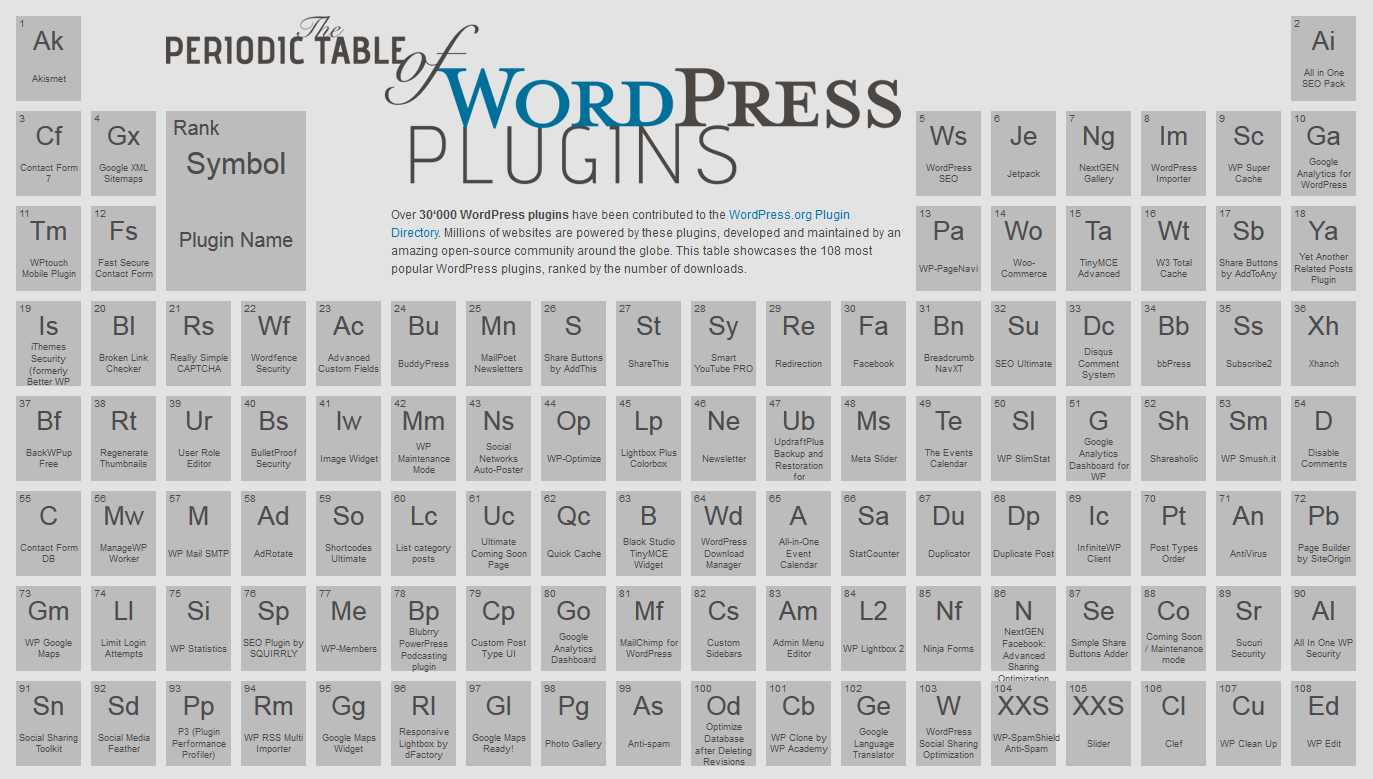
My natural starting point is yet again WordPress. WordPress’ biggest selling point is, in my humble opinion, the astonishingly huge selection of free plugins available from the WordPress.org repository. While one shouldn’t simply ignore the importance of the WordPress core itself as well as the ease with which one can change up your design with themes, it is plugins that equip us with the ability to achieve just about anything.
You may well have come across lists of the most popular WordPress plugins before, ( I have listed some in my previous blog post) but probably nothing quite like the periodic table of WordPress plugins.
When hearing “WordPress” the first association many would make is “top website building application”, “endless enhancement possibilities” or “best blogging platform”. Yet there are some that would say “security vulnerabilities” is the first thing that springs to mind. Sadly, they won’t be very far from the truth. Due to the open-source nature of the script, pretty much everyone can contribute to the WordPress project. As good as that is for providing more and more extras, this also creates many hacking opportunities because of badly written plugins and themes. And this is actually how most WordPress websites get hacked. So, in order to save you some headaches, here is a list that will at least raise your awareness as to which plugins you should be wary of. I explicitly want to stress the importance of keeping ALL your plugins and themes constantly updated to minimize the risk of any possible breaches. Even if you don’t find your plugins in this list, it is best to keep yourself and your WP website on the safe side.
1. TimThumb – this image resizing/cropping/editing tool has been unlucky for years now. After some major attacks back in the days, all seemed fine for a while but a new zero-day vulnerability was recently discovered again. When its “WebShot” feature is enabled, it widely opens its gates for hackers to create, remove or modify files on your server without authorization.
2. All In One SEO Pack – another unlucky victim of many attacks through the years. An even more alarming fact is that this is one of the most popular SEO plugins for WordPress so a lot of people are at risk. In the end of May two new security loopholes were found. They allow the attacker to perform XSS attacks and change privilege escalations. In the latest version released this should already be fixed.
3. MailPoet – formerly known as WYSIJA Newsletters, this plugin has been downloaded over 1.7 million times. A recent breach of security was found, where an user can upload a PHP file without any user permissions. Needless to say this creates a perfect environment for attackers to send spam, put malicious codes and other types of malware. The only recommended safe version is 2.6.7.
4. WP Touch – unfortunately this cool mobile plugin which lets you easily create themes for your WordPress website, is also in the list with a very recent exploit. A vulnerability was found (though affecting only websites that allow guest users to register) that allows hackers to easily upload a PHP backdoor or other pieces of malware through the so-called “nonce”.
5. Disqus – again a very popular plugin that suffered through a fair share of attacks. The latest vulnerability is pretty specific and it can only harm websites using PHP version 5.1.6 or earlier (or WordPress version 3.1.4 or earlier, respectively). Remember what we said earlier about regular updates? 🙂
6. OptimizePress – bad news for mobile users of this plugin. It does not pose a threat for PC users and visitors, but the ones on a mobile device are not safe. The exploit recognizes the location of the visitor and redirects them to other websites which can include fake sites requiring payment, fake security websites, porn sites etc.
7. JW Player – one of the WP video player plugins. It was recently disclosed that versions 5.10.2393 and earlier are open to content spoofing and cross-site scripting (XSS) vulnerabilities. That’s some bad news considering that there were similar loopholes in earlier versions who were supposed to be fixed.
8. Login Rebuilder – one that is very sweet for anyone that wants to perform a cross-site request forgery attack. Once the attack is activated, the victim is practically “forced” to perform operations on behalf of the attacker.
9. Duo Two-Factor Authentication – ironically, security plugins are not immune to vulnerabilities either. After previous attacks on Better WP Security and WordFence, a recent case dating a couple months back shows, that the Duo plugin had some troubles with WP multisites, letting a shop owner bypass the second level of security and gain access to the other shops in the same network. This was fixed in version 2.2 of the plugin, so if you have an older one make sure to update it.
10. XCloner – a backup and restore module that was also breached a few months ago, leaving it prone to CSRF attacks. The vulnerability was later cleared but all versions prior of 3.1.0 still pose a security risk.
The list is compiled with popular plugins as it is more likely that many people are using them. You can imagine just how much of an impact those might have created and this should serve as a reminder that nothing is safe if you just let it go on autopilot. As an owner of a WordPress website you are also responsible of keeping an eye on important notifications and updates and do what you can to minimize risks. Hope that list helps and I welcome you to share your experiences and tricks on making your WP site secure in the comments below.